Wealth Management Solution Systems
State of the Art Reporting
for Family offices
and Wealth Managers

locations
Active End-clients
Assets under Reporting
UNIQUE ASSETS
TRACKED
aggregated custodians
Savvy Advisors and Intelligent Investors Use Canopy
Manual data entry, inaccurate data consolidation and amateurish reports are all things of the past.
Consolidate PDF and electronic data for all types of assets, including structured products, private equity, real estate etc.
Sophisticated and intuitive tools to instantly slice and dice clean data flexibly to obtain actionable insights.
One size almost never fits all. We customize professional reports according to your requirements for all your reporting needs.








Data Security is of Utmost Importance
Canopy meets international information security standards and is IS0-27001 certified.
All our databases are encrypted with 256-bit keys (AES-256). Industry consensus is that it would take a supercomputer millions of years to crack the encryption via a brute force attack.

All data sent to the web browser is encrypted (with technology such as HTTPS). This means that third parties need to break the encryption to see what is being sent to your browser.

We regularly engage professional ethical hackers to try, and break into our infrastructure and assess all security aspects.

We use active monitoring tools that ensure all our software code matches the highest security standards.

Our infrastructure is secured behind advanced firewall systems. We also have high-end anti-virus and anti-malware scanning our systems.
.svg)
We practice two factor authentification. 2FA provides an additional layer of security beyond strong passwords.
A family office and wealth managment software Trusted by Top Private Banks and Advisors
Intuitive, flexible and comprehensive for all types of users.


Canopy Manager enables wealth managers to perform advanced analysis across clients and deepen client engagement..
- Collectively review multiple client portfolios at one go
- Calculate the performance on any basket of transactions you create
- Order or design your own high-end customized reports


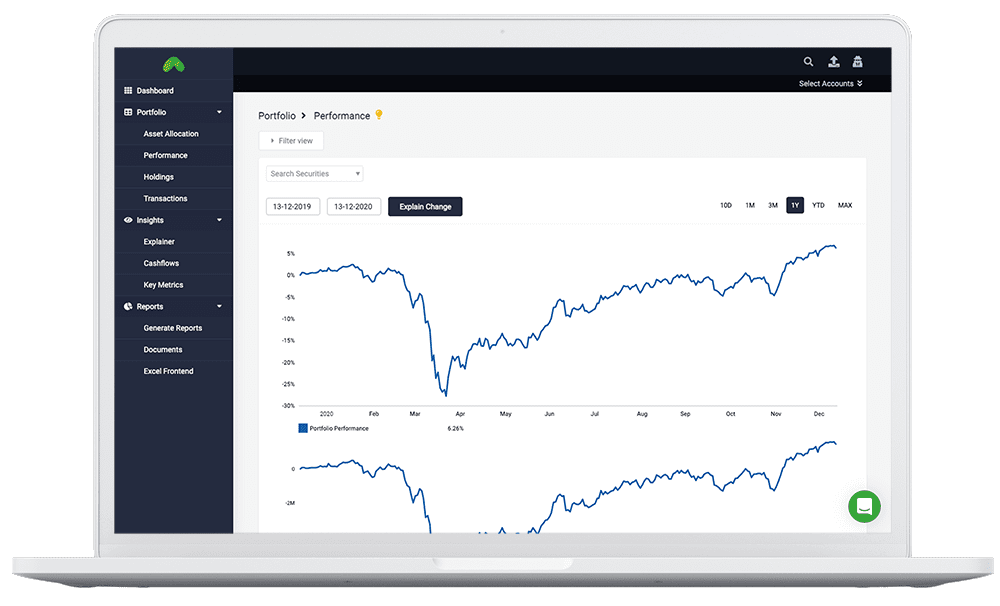
An intuitive and interactive web application that allows the user to view their consolidated portfolio.
- Secure access via mobile phone or computer
- Customizable asset classifications
- View combination of accounts and securities
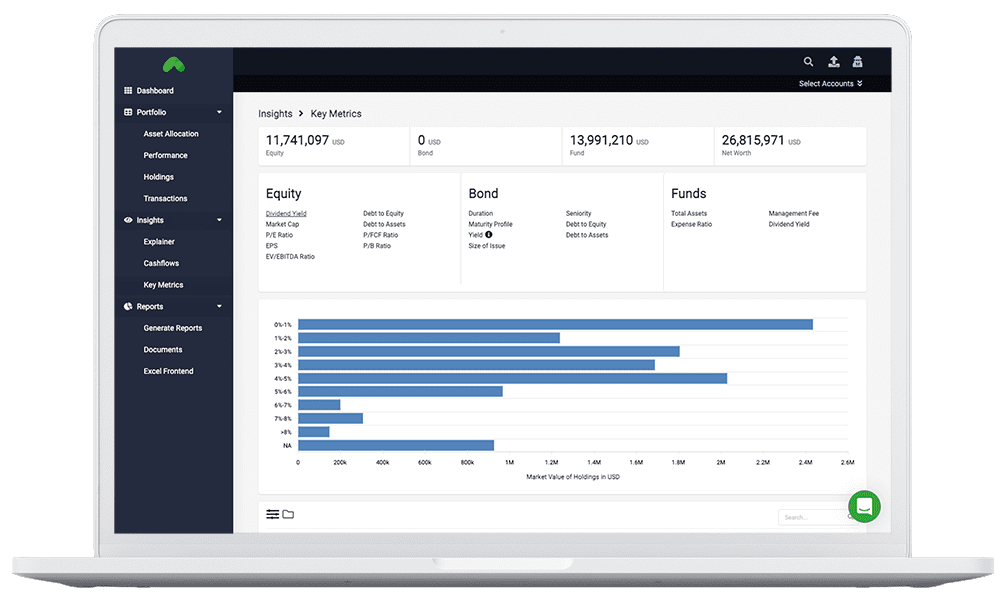

The Canopy Analytics module allows for custom analytics and complete access to the enriched data.
- Custom performance and risk analytics
- Cashflows calculations
- Key financial metrics with a single click

The Canopy Reporter allows users to generate consolidated or individual account reports with the click of a button.
- Export in Powerpoint or PDF
- Generate template or custom reports
- High-level summaries or detailed analytics
Some of our Prestigious Clients Worldwide
We serve 4 of the 20 wealthiest family offices as ranked by Bloomberg.

Speak to Us
Kindly allow for 2 working days for response.
Singapore (HQ)
Canopy Pte. Ltd.
11 Irving Place #09-01 Singapore 369551
+65 8265 5358
ZURICH
Canopy Europe AG
Rigistrasse 2, 6300 Zug - Switzerland
+41 44 586 0012
NEW YORK
Canopy.Cloud Inc.
99 Hudson Street, 5th Floor
New York NY 10013
Connect via email at hello@canopy.cloud
FREQUENTLY ASKED Questions
If you have any further questions, feel free to get in touch with our team.

Custodians with a direct datafeed
The list of custodians with a datafeed connection to Canopy is updated regularly here. Typically a setup fee and monthly maintenance charges apply for datafeed integrations. Credit Suisse clients, however, can enjoy certain datafeeds for free.

Types of assets Canopy can accept
Canopy can process data for all financial and non-financial assets. This includes private equity, real estate, wine and collections and more.

Format of data to be provided
Canopy accepts data in computer-generated PDF format, excel, and data delivered through datafeeds. We do not accept scanned PDF statements due to data inaccuracies stemmings from low-quality scans.

Features included in Canopy Subscription
Simply put, your Canopy Subscription includes all the features available in a Canopy Demo account. Do not hesitate to request for a free Demo account for clarity. The subscription fee does not include customized features and dashboards not available in the Demo account.

Turnaround time for data processing
The turnaround time for datafeed processing is 1 working day. For ePDF processing, the processing time varies between 3-5 working days.

Adding transactions to Canopy myself
The Self-service module is currently being built.

Languages supported
English, Simplified Chinese, Traditional Chinese and German


